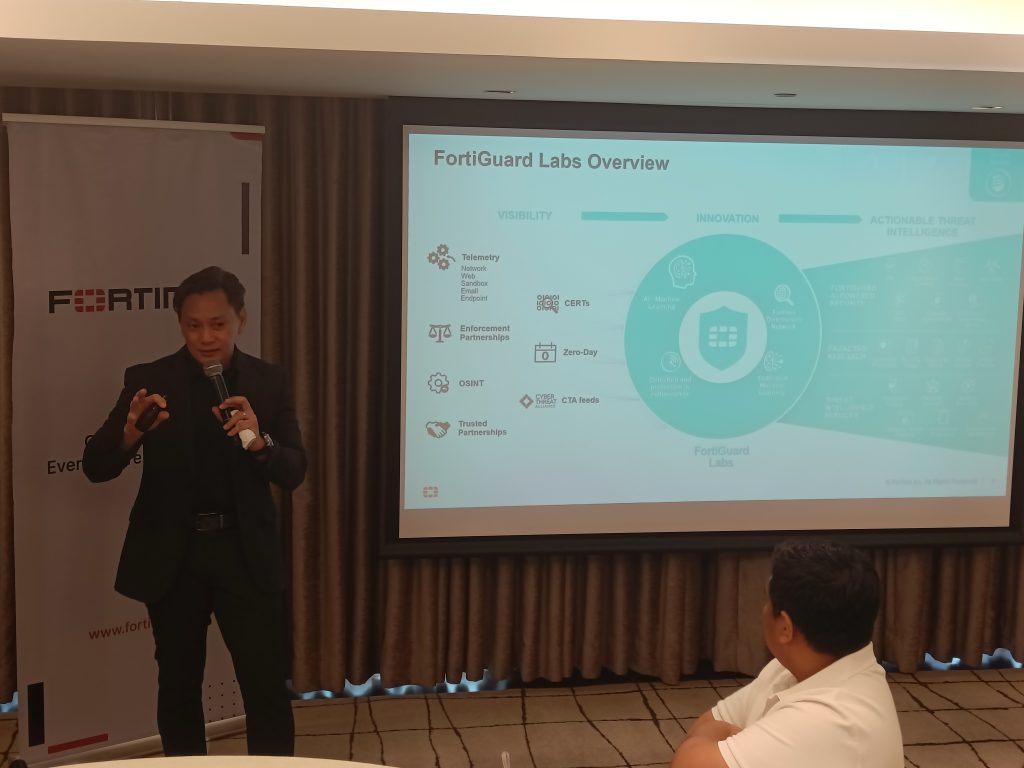
Fortinet, the global cybersecurity leader driving the convergence of networking and security, today announced the latest semiannual Global Threat Landscape Report from FortiGuard Labs. During a recent press briefing held at the New World Makati Hotel, Alan Reyes, Country Manager of Fortinet Philippines, shared key insights from FortiGuard Labs’ Q2 2023 Threat Report. This report provides organizations with valuable intelligence on potential threat activities.
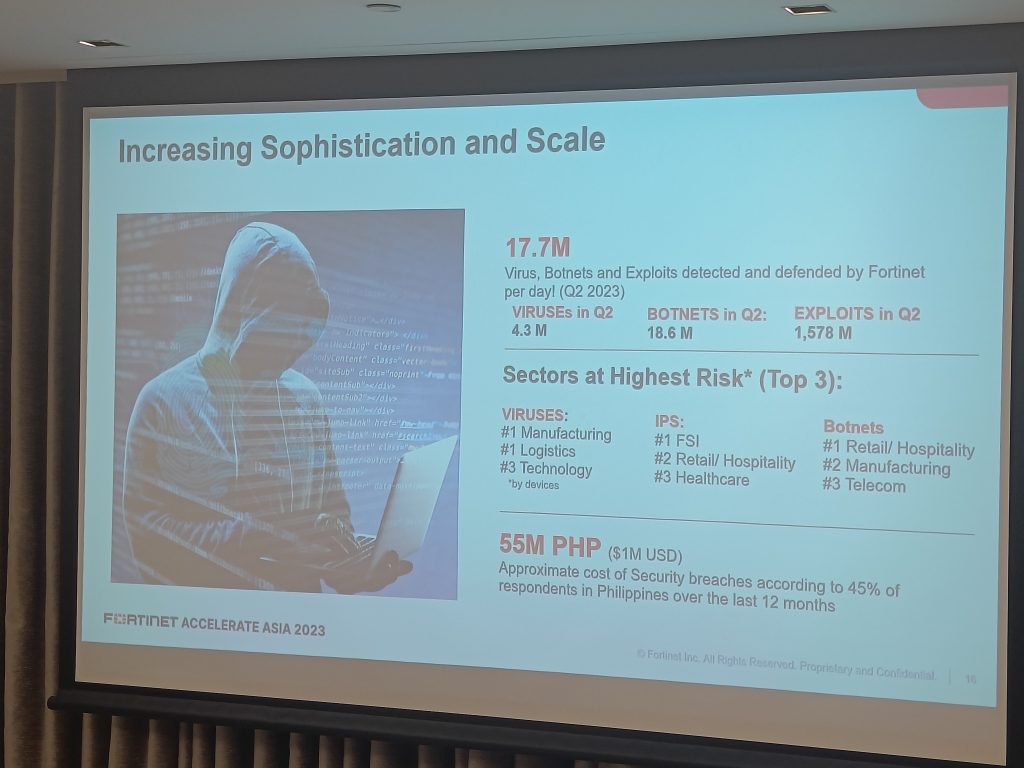
In the first half of 2023, FortiGuard Labs observed notable trends, including a decrease in ransomware detections, heightened activity among advanced persistent threat (APT) groups, shifts in MITRE ATT&CK techniques used by attackers, and more. Beyond the highlights mentioned here, the comprehensive analysis is available in the 1H 2023 Global Threat Landscape Report. The report also revealed that Fortinet successfully identified and defended against approximately 17.7 million viruses, botnets, and exploits per day in the Philippines during Q2 2023.
Reyes emphasized that the distribution of threats in Q2 2023 remained relatively consistent compared to the previous quarter. He noted, “The Asia-Pacific (APAC) region contributed to approximately 25 to 33% of the global telemetry data. However, our threat report underscored the significant number of viruses, botnets, and exploits encountered regularly. This highlights the urgent need for organizations to bolster their cybersecurity strategies to strengthen their defenses, especially in light of the growing sophistication and frequency of threats.”
Highlights of the report follow
Organizations Detecting Ransomware Are on the Decline
FortiGuard Labs has documented substantial spikes in ransomware variant growth in recent years, largely fueled by the adoption of Ransomware-as-a-Service (RaaS). However, FortiGuard Labs found that fewer organizations detected ransomware in the first half of 2023 (13%) compared to this time five years ago (22%). This supports the trend that FortiGuard Labs has seen over the last couple of years, that ransomware and other attacks are becoming increasingly more targeted thanks to the growing sophistication of attackers and the desire to increase the return on investment (ROI) per attack. Research also found that the volume of ransomware detections continues to be volatile, closing 1H 2023 13x higher than the end of 2022 but still on a downward trend overall when comparing year-over-year.
Malicious Actors Are 327x More Likely to Attack Top EPSS Vulnerabilities within Seven Days Compared to All Other CVEs
This project aims to leverage a myriad of data sources to predict the likelihood and when a vulnerability will be exploited in the wild. FortiGuard Labs analyzed six years of data spanning more than 11,000 published vulnerabilities that detected exploitation and found that the Common Vulnerabilities and Exposures (CVEs) categorized with a high EPSS score (top 1% severity) are 327x more likely to be exploited within seven days than any other vulnerability.
Nearly One-Third of APT Groups Were Active in 1H 2023
For the first time in the history of the Global Threat Landscape Report, FortiGuard Labs tracked the number of threat actors behind the trends. Research revealed that 41 (30%) of the 138 cyberthreat groups MITRE tracks were active in the 1H 2023. Of those, Turla, StrongPity, Winnti, OceanLotus, and WildNeutron were the most active based on malware detections. Given the targeted nature and relatively short-lived campaigns of APT and nation-state cyber groups compared to the long life and drawn-out campaigns of cybercriminals, the evolution and volume of activity in this area will be something to look forward to in future reports.
Five-Year Comparison Reveals Explosion in Unique Exploits, Malware Variants, and Botnet Persistence
Unique Exploits on the Rise: In 1H 2023, FortiGuard Labs detected more than 10,000 unique exploits, up 68% from five years ago. The spike in unique exploit detections highlights the sheer volume of malicious attacks security teams must be aware of and how attacks have multiplied and diversified in a relatively short amount of time. The report also shows over a 75% drop in exploitation attempts per organization over a five-year window and a 10% dip in severe exploits, suggesting that while malicious actor exploit toolkits have grown, the attacks are much more targeted than five years ago.
Malware Families and Variants Exploded, Up 135% and 175%, Respectively
The number of malware families that propagate to at least 10% of global organizations (a notable prevalence threshold) has doubled over the last five years. This escalation in malware volume and prevalence can be attributed to more cybercriminal and APT groups expanding operations and diversifying their attacks in recent years. A significant focus of the last Global Threat Landscape report was the surge in wiper malware largely tied to the Russian-Ukraine conflict. That increase persisted throughout 2022 but slowed over the first half of 2023. FortiGuard Labs continues to observe wipers being used by nation-state actors, although the adoption of this type of malware by cybercriminals continues to grow as they target organizations in technology, manufacturing, government, telecommunications, and healthcare sectors.
Botnets Lingering in Networks Longer Than Ever
While the report finds more active botnets (+27%) and a higher incidence rate among organizations over the last half-decade (+126%), one of the more shocking findings is the exponential increase in the total number of “active days”, which FortiGuard Labs defines as the amount of time that transpires between the first hit of a given botnet attempt on a sensor and the last. Over the first six months of 2023, the average time botnets lingered before command and control (C2) communications ceased was 83 days, representing over a 1,000x increase from five years ago. This is another example where reducing the response time is critical because the longer organizations allow botnets to linger, the greater the damage and risk to their business.
Disrupting Cybercrime Requires an All-in Approach
FortiGuard Labs’ contributions to the threat intelligence community over the last decade have made significant impacts around the globe, helping to improve protections for customers, partners, and governments in their fight against cybercrime. Breaking down silos and increasing the quality of actionable threat intelligence helps organizations reduce risk and enhances the overall effectiveness of the cybersecurity industry. Cyber defenders today currently possess access to the tools, knowledge, and support to begin altering the economics of malicious actors. Still, it’s an industrywide commitment to collaboration and intelligence sharing that will ultimately create a larger ecosystem of disruption and allow the industry to gain the upper hand against cyber adversaries.
As a leader in enterprise-class cybersecurity and networking innovation, Fortinet helps secure over half a million organizations worldwide, including global enterprises, service providers, and government organizations. Of note, Fortinet’s ongoing development of artificial intelligence (AI) applied to cybersecurity use cases, in both our FortiGuard Labs and product portfolio, is speeding the prevention, detection, and response to known and unknown threats.
Specifically, FortiGuard AI-Powered Security Services are utilized by security controls deployed across endpoints and applications through both network and cloud infrastructure. Purpose-built detection and response technologies that leverage AI engines and cloud analytics (including EDR, NDR, and others) can also be deployed as integrated extensions of such controls. Fortinet also offers centralized response tools, such as XDR, SIEM, SOAR, DRPS, and more, that leverage different AI, automation, and orchestration to speed remediation. These can all significantly disrupt cybercrime across the entire attack surface and along the cyberattack kill chain.
Philippines, Q2 2023
The latest findings from FortiGuard Labs reveal that Excel and Microsoft Intermediate Language (MSIL) malware variants have emerged as the predominant cybersecurity threats across the Asia-Pacific (APAC) region during the second quarter of 2023. These malware types stand out due to their adaptability and versatility in creating various forms of malicious software. Excel malware, often disseminated through phishing emails containing malicious macros, remains a prevalent attack vector. Meanwhile, MSIL, a bytecode format utilized by the .NET framework, proves to be highly modifiable, adding to its threat potential.
In the Philippines, the FortiGuard Labs team detected a staggering 4.3 million instances of viruses. Notably, the JS/Agent,Cy!tr virus emerged as the most prominent, contributing to 3.5% of viruses detected within the quarter. It was closely followed by HTML/Agent.ROUT!phish, which accounted for 3.2% of the detected viruses.
In addition, with botnet activities during the first quarter of 2023, the Philippines faced significant challenges from Mirai, Ghost Rat, Bladabindi, Mozi, and RotaJakiro botnets. These malicious networks were responsible for a range of nefarious activities, including distributed denial-of-service (DDoS) attacks, credential harvesting, and data exfiltration. FortiGuard Labs recorded a total of 18.6 million botnet attacks, with Mirai and Gh0st.rai being the predominant threat, representing 16% of all observed botnet activity in the quarter.
These findings underscore the need for businesses in the Philippines and individuals to remain vigilant and proactive in fortifying their cybersecurity defenses against the evolving threat landscape, reinforcing the importance of timely patching and the deployment of robust security measures.
Report Overview
This latest Global Threat Landscape Report is a view representing the collective intelligence of FortiGuard Labs, drawn from Fortinet’s vast array of sensors collecting billions of threat events observed around the world during the first half of 2023. Using the MITRE ATT&CK framework, which classifies adversary tactics, techniques, and procedures, the FortiGuard Labs Global Threat Landscape Report describes how threat actors target vulnerabilities, build malicious infrastructure, and exploit their targets.
Meet with Fortinet at Black Hat USA
Meet Fortinet’s team of experts at booth #1240. A wide range of products, services, and threat intelligence and response solutions will be on display for attendees. Read the blog for more information.